(Updated Nov. 7, 2014)
The Centers for Disease Control and Prevention reported on Nov. 4 that the death toll from the Ebola outbreak in West Africa has risen to above 4,960 and that an estimated 8,168 people, mostly in Liberia, Sierra Leone and Guinea, have contracted the virus since March. It is the largest and most severe outbreak of the Ebola virus since it was first detected four decades ago. All but nine of the deaths were in those three countries; eight were in Nigeria and one patient died in the United States.
The CDC in October proclaimed that in the worst-case scenario, Sierra Leone and Liberia could have 1.4 million cases by Jan. 20, 2015, if the disease keeps spreading without immediate and immense intervention to contain the virus.
Two American aid workers infected with Ebola while working in West Africa were transported to a containment unit at Emory University in Atlanta for treatment, raising public fears about international spread of the highly virulent virus that has no known cure. The two were released from the hospital after being the first humans to receive an experimental Ebola drug called ZMapp. Another man who recently helped an Ebola victim in Liberia traveled to Texas and died in a Dallas hospital. Two of the nurses who treated him caught the virus as well, but have been released from the hospital. Some states have struggled with the moral
We ask CISAC biosecurity experts David Relman and Megan Palmer to answer several questions about Ebola and the public health concerns and policy implications. Relman is the co-director of the Center for International Security and Cooperation who has served on several federal committees investigating biosecurity matters. He is the Thomas C. and Joan M. Merigan Professor in the Departments of Medicine and of Microbiology and Immunology at Stanford University School of Medicine, and Past-President of the Infectious Diseases Society of America.
Palmer is the William J. Perry Fellow in International Security at CISAC and a Researcher at the UC Berkeley Center for Quantitative Biosciences (QB3), and served as Deputy Director of Policy & Practices for the Multi-University NSF Synthetic Biology Engineering Research Center (SynBERC).
The two of them have answered the questions together.
What is Ebola and how dangerous is it compared to other diseases?
Ebola is an acute viral infectious disease, often associated with severe hemorrhagic fever. While initial symptoms are flu-like, they can rapidly progress, and include vomiting, reduced ability to regulate immune responses and other physiological processes, sometimes leading to internal and external bleeding. The disease has an incubation period that can last up to 21 days, but patients typically become ill four to nine days after infection, and die about seven to ten days later. Fatality rates for the current Ebola outbreak are nearing 60% (according to the CDC), while past outbreaks in the Republic of Congo have seen rates as high as 90%. This outbreak to date has resulted in nearly 1,000 deaths, more than any previous Ebola outbreak.
Ebola virus is believed to reside in animals such as fruit bats where it does not cause disease, but is then transmitted to and among humans and other primates, in whom disease typically does occur. The route by which the virus crosses between species remains largely unknown. People become infectious once they become symptomatic. Ebola is transmitted via blood or bodily fluid, but can persist outside the body for a couple days. Infection can occur through unprotected contact with the sick, but also when contaminated equipment such as needles cut through healthcare workers’ protective gear, and also through contact with infected individuals postmortem.
 |
|
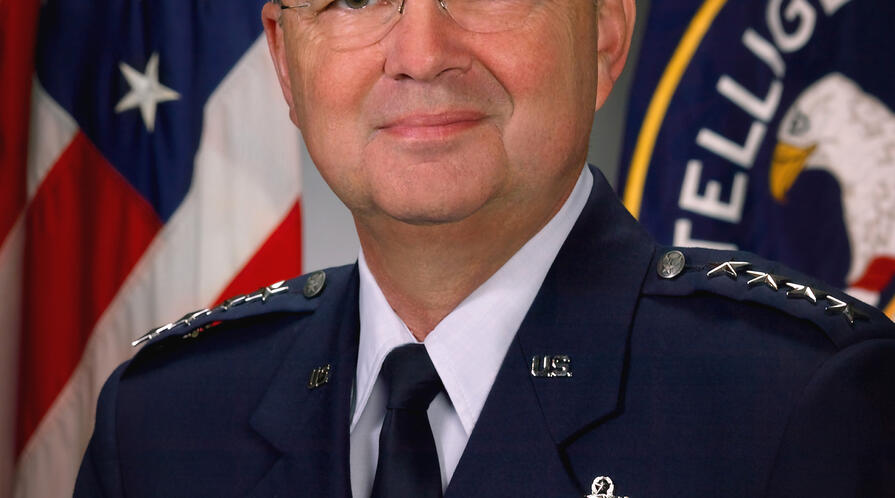
David Relman
Photo Credit: Rod Searcey
|
Ebola’s horrific symptoms provoke public fear, and it becomes easy to lose perspective on the relative spread and toll of this outbreak. Ebola is relatively difficult to transmit. This means the latest Ebola outbreak is still small in comparison to the hundreds of thousands of people killed each year via more easily transmitted airborne influenza strains and other diseases such as malaria and tuberculosis. It’s important that we not lose sight of more chronic, but less headline-grabbing diseases that will be pervasive, insidious long-standing challenges for Africa and elsewhere.
Is there a vaccine or cure?
There is no vaccine for Ebola and no tried-and-true cure. Health workers can only give supportive care to patients and try to stop the spread to new victims.
Several experimental therapies for Ebola are under development. One receiving attention is ZMapp, a mix of antibodies produced by mice exposed to the virus that have been adapted to improve their human compatibility. Limited tests in primates show early promise, but the drug had not been tried on humans -- until now. Two Americans transported back to the U.S. from West Africa received the experimental therapy. While the two seem to be improving, it isn’t clear that ZMapp was responsible; another issue is that ZMapp and other potential therapies have not been cleared by the FDA for wider use in humans.
The process for approval, and who gets priority access to such drugs, are complex policy issues. The WHO will be convening leaders and medical ethicists next week to discuss how to develop and distribute experimental therapies. This is not a simple task; many factors need to be taken into consideration and balanced with limited information to guide decisions.
Successful or not, and despite any approval, it’s still uncertain whether enough of such drugs could even be produced quickly enough to respond to this particular outbreak, and if not - whether they’d be effective in a future outbreak.
You can listen to Relman in this KQED Public Radio talk show.
Relman joins other experts in a Stanford panel on Ebola
Why has this Ebola outbreak involved so many more people, and spread to a wider geographic area, than previous outbreaks?
This is an evolving investigation and many potential contributing factors are being examined by scientists racing to collect information that can help them get ahead of the outbreak.
One factor is population density. This latest outbreak spread early into denser population areas within Liberia and Sierra Leone, rather than remain confined to isolated villages, as in earlier outbreaks in Central Africa. With a greater number of people being exposed within a smaller geographic area, the likelihood of transmission increases. Of particular concern is the prospect that the virus might take hold in Lagos, Nigeria, where a handful of cases have been recently identified. If this were to spread in Lagos, Africa’s most populous city, the death toll would likely increase dramatically.
Another factor is the ability of affected regions to mount an effective public health response. This outbreak is occurring in three of the poorest African countries: Sierra Leone, Liberia, and Guinea. Civil wars have likely contributed to degradation of an already relatively poor public health infrastructure. This is also the first Ebola outbreak in the region, and the inexperience of local authorities can delay responses and fuel fearful community responses, undermining the ability to deal with the outbreak early when it’s more easily contained.
Cultural practices around the care of the sick and the dead can also fuel progression of an outbreak. In some parts of Western Africa, washing deceased relatives is commonplace. Customs like these increase the likelihood of the infection spreading through proximity between infected individuals and their family members
What can be done to curtail the outbreak?
Isolation and quarantine are key to fighting the spread of Ebola. Isolation involves removing infected individuals from the general population to prevent the spread of disease. Quarantine, however, involves removing uninfected or potentially infected individuals from the general population to limit the spread of disease.
Thus far, the strategy to fight Ebola is dependent on isolating infected patients. Unsurprisingly, isolation efforts have proven hard to enforce. Some families, faced with the prospect of being confined to their homes, have denied the existence of Ebola in their localities, or refuted doctors who claim that one of their family members is sick. This is not unique to Africa; Americans had violent reactions to quarantine during the spread of smallpox. Some regions are now taking more extreme measures: Sierra Leone has deployed its army to enforce isolation at clinics and infected families’ homes, but this also risks civil unrest.
These tensions underscore the necessity of improved education and enforcement mechanisms within public health strategies. Response measures involve fundamental tradeoffs between liberty and safety. Because negotiations occur through complex local, national and international processes, one of the biggest risks is that decisions don’t keep pace with disease spread.
It’s important that we not lose sight of more chronic, but less headline-grabbing diseases that will be pervasive, insidious long-standing challenges for Africa and elsewhere."
How likely is it that the disease will spread into and within the United States?
Currently, airports in Liberia, Sierra Leone, and Guinea are screening all outbound passengers for Ebola symptoms such as fever. This includes asking passengers to complete healthcare questionnaires. However, it is difficult to reliably know who has been infected until they are symptomatic. Individuals could theoretically board a plane before they show symptoms, but develop them upon landing in the United States or elsewhere. This makes containing Ebola difficult, but not impossible.
If the virus were to enter the United States, it would be easier to contain and harder to spread. This virus does not transmit that easily to other humans, especially in settings with good infection control and isolation.
As viruses spread, the chances of genetic variation increase. Yet despite all the concerns from the current outbreak, Ebola is relatively bad at spreading in comparison to respiratory viral diseases such as influenza or measles. The likelihood of a pandemic Ebola virus in the near future seems slim as long as it cannot be transmitted via air. While it’s possible that the Ebola virus could evolve, there is little evidence to suggest major genetic adaptations at this time.
What are some broader lessons about the dynamics and ecology of emerging infectious diseases that can help prevent or respond to outbreaks now and in the future?
These latest outbreaks remind us that potential pathogens are circulating, replicating and evolving in the environment all the time, and human action can have an immense impact on the emergence and spread of infectious disease.
We are starting to see common factors that may be contributing to the frequency and severity of outbreaks. Increasing human intrusion into zoonotic disease reservoir habitats and natural ecosystems, increasing imbalance and instability at the human-animal-vector interface, and more human population displacement all are likely to increase the chance of outbreaks like Ebola.
 |
|
Megan Palmer
Photo Credit: Rod Searcey
|
The epicenter of this latest outbreak was Guéckédou, a village near the Guinean Forest Region. The forest there has been routinely exploited, logged, and neglected over the years, leading to an abysmal ecological status quo. This, in combination with the influx of refugees from conflicts in Guinea, Liberia, Sierra Leone, and Cote d’Ivoire, has compounded the ecological issues in the area, potentially facilitating the spread of Ebola. There seems to be a strong relationship between ecological health and the spread of disease, and this latest outbreak is no exception.
While forensic analyses are ongoing, unregulated food and animal trade in general is also a key factor in the spread of infectious diseases across large geographic regions. Some studies suggest that trade of primates, including great apes, and other animals such as bats, may be responsible for transit of this Ebola strain from Central to Western Africa.
What are some of the other political and security implications of the outbreak and response?
Disease outbreaks can catalyze longer-term political and security issues in addition to more acute tensions.
There are complex international politics involved in emergency response and preparedness. Disease outbreaks often occur in poor regions, and demand help from more wealthy regions. The nature of the response reflects many factors - technical, social, political, legal and economic. Leaders often lack the expertise to take all these factors into account. It is an ongoing challenge to adapt our governance processes to be more reliable and move from damage control to planning. Organizations like the World Health Organization can provide guidance, but more resources and expertise are needed to get ahead of future disasters.
When help is provided, there is often mistrust of non-local workers, who can even be seen as sources of the disease. At a political level, distrust has been fueled by disguising political missions as health interventions, as was the case with the effort that led to the locating of Osama Bin Laden.
There are other security implications of this latest epidemic. This outbreak has led to a dramatic increase in the availability of Ebola virus in unsecured locations across West Africa, as well as to a growing number of labs across the world studying the disease. The immediate need to study the disease and develop beneficial interventions needs to be coupled to considerations of safety and security. From a safety standpoint, a rise in the handling of Ebola samples risks accidental transmission. From a security standpoint, those who wish to cause harm with this virus could acquire it from bodies, graves and other natural sources in the affected region. Both of these risks demand attention and efforts at mitigation.







 Facebook CSO Joe Sullivan addresses the boot camp, Aug. 20, 2014.
Facebook CSO Joe Sullivan addresses the boot camp, Aug. 20, 2014.


 Cybersecurity fellow Jonathan Mayer to teach online class on surveillance.
Cybersecurity fellow Jonathan Mayer to teach online class on surveillance.




